Listen
- https://open.spotify.com/track/65GbQI9VDTs7vo6MJL2iJA (open.spotify.com)
Episode summary: "The future of Bitcoin, as envisioned through Snowden's lens, is not just a technological revolution but a societal transformation where "decentralized systems" empower us against the omnipresent specter of institutional and governmental co
Watch:streamable.com
"The future of Bitcoin, as envisioned through Snowden's lens, is not just a technological revolution but a societal transformation where "decentralized systems" empower us against the omnipresent specter of institutional and governmental control." - Edward Snowden On Bitcoin
It's been a week! The silent war of surveillance is at our doorstep, and it's being gathered whether you like it or not. The discourse around surveillance, privacy, and emerging technologies like Bitcoin and AI is relevant and crucial. It's also been on the top of my mind in conversations I have been having this weekend. We live in a digital era, where every byte of personal information can be considered currency, data, or viewed as a threat to the state.
Are we already living in this Orwellian world?
Yes, we are.
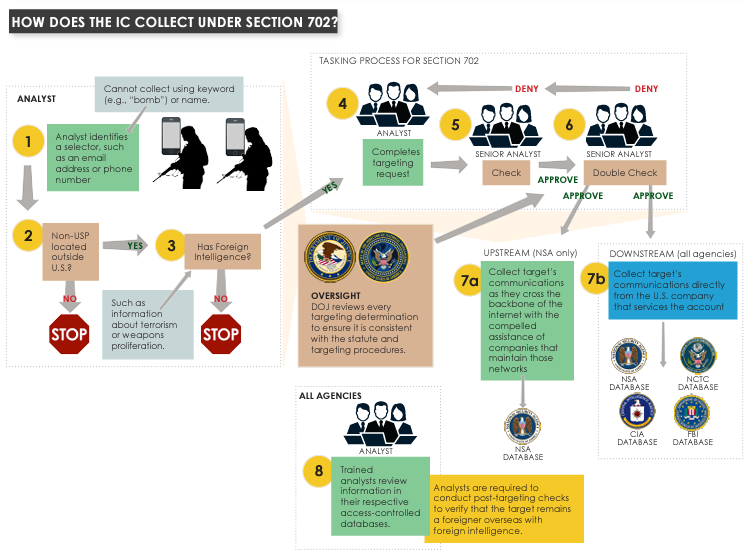
After Edward Snowden leaked NSA slides in 2013, two names became synonymous with the agency’s vast online spying powers: Upstream and PRISM. Both also fall under a surveillance authority known as Section 702 , a provision of law that was enacted by the FISA Amendments Act of 2008. In early 2017, the intelligence community rebranded these two kinds of surveillance, referring to them as “upstream” and “downstream.” The names may have changed, but the surveillance is the same. Upstream surveillance involves collecting communications as they travel over the Internet backbone, and downstream surveillance (formerly PRISM) involves collection of communications from companies like Google, Facebook, and Yahoo. - Upstream vs. PRISM
While regulatory bodies and institutions cast a looming shadow over the development and utilization of bitcoin, Snowden's encouragement to focus on influenceable areas and pioneer unowned and private systems is perfectly timed as Congress is set to reauthorize Section 702 of the Foreign Intelligence Surveillance Act (FISA) by the end of the year.
FOREIGN INTELLIGENCE SURVEILLANCE ACT - SECTION 702
In 2008, Congress enacted Section 702 of the Foreign Intelligence Surveillance Act (FISA), a critical intelligence collection authority that enables the Intelligence Community (IC) to collect, analyze, and appropriately share foreign intelligence information about national security threats. Section 702 authorizes targeted intelligence collection of specific types of foreign intelligence information—such as information concerning international terrorism or the acquisition of weapons of mass destruction—identified by the Attorney General and the Director of National Intelligence (DNI).
Section 702 only permits the targeting of non-United States persons who are reasonably believed to be located outside the United States. United States persons and anyone in the United States may not be targeted under Section 702. Section 702 also prohibits “reverse targeting”—the IC may not target a non-U.S. person located outside the U.S. if the purpose of the collection is to collect information about a United States person or anyone located in the United States.
Section 702 is not a bulk collection program; it is a substantial and important targeted intelligence collection program. Every Section 702 targeting decision is individualized and documented, approved pursuant to a multi-step process embodied in specific targeting procedures, and reviewed by an independent oversight team.
Although all Section 702 targets must be non-United States persons reasonably believed to be located outside the United States, Congress has always recognized that such targets may send an email or have a phone call with a United States person. For this reason, Section 702 requires specific procedures to minimize the acquisition, retention, and sharing of any information concerning United States persons. “Minimize,” however, does not always mean “eliminate” – if, for example, a foreign terrorist indicated that a United States person was a key member of an ongoing terrorist plot, this information would be appropriately shared to allow the FBI to take further investigative steps. Congress also amended Section 702 to require specific procedures to ensure the querying of any Section 702-acquired information is consistent with the Fourth Amendment.
The Section 702 program is subject to extensive oversight. The Attorney General must approve the targeting, minimization, and querying procedures, each of which are annually reviewed by the Foreign Intelligence Surveillance Court (FISC) for consistency with the FISA statute and the Fourth Amendment. Each of the IC elements involved in the Section 702 program has developed internal oversight processes and programs to ensure compliance with these procedures. The Department of Justice and the Office of the Director of National Intelligence conduct extensive, regular, and independent reviews of Section 702 activities. Any identified compliance errors are remedied and reported to the FISC and Congress.
The interesting thing about Section 702 is that it allows collection only against targeted foreigners overseas but stipulates that those foreigners may communicate with Americans. In those situations, it further explains "Querying Procedures."
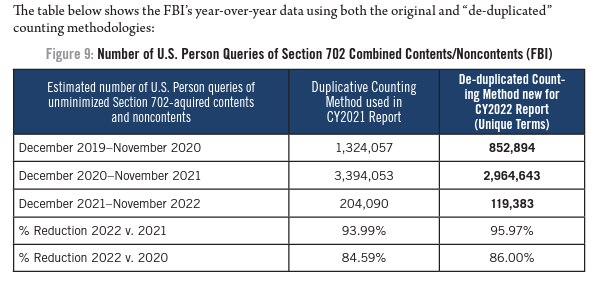
Query terms may be date-bound and may include alphanumeric strings (e.g., telephone numbers or email addresses) or terms (e.g., the name of a person or company) that can be used individually or in combination with one another. Pursuant to FISC-approved procedures, an agency can only query Section 702 information if the query is reasonably likely to retrieve foreign intelligence information or, in the case of the FBI, evidence of a crime. This standard applies to all Section 702 queries, regardless of whether the term concerns a U.S. person or non-U.S. person. The 2020 querying procedures were released in April 2021. Querying procedures were approved in April 2022 and April 2023 but have not yet been publicly released.
The President's Intelligence Advisory Board has already reviewed and underscored the urgency to reauthorize this provision swiftly. Remarks are coming inbound as well as outside on the matter.
The "upstream" surveillance program Snowden exposed showcases the government's adept skill in utilizing "state secrets" to smokescreen its potentially unconstitutional endeavors.
While regulatory bodies and institutions cast a looming shadow over the development and utilization of bitcoin, Snowden's encouragement to build, innovate, and challenge established systems— is not just a sound directive for the bitcoin community but also a universal plea to fight for the liberties and privacies we are currently losing.
In the light of the golden path, hope and pain start looking the same.